Join War on the Rocks and gain access to content trusted by policymakers, military leaders, and strategic thinkers worldwide.


Would you trust a Reaper crew to keep you safe in the face of enemy fire? In their Foreign Affairs article, “Why Troops Don’t Trust Drones,” Jacquelyn Schneider and Julia MacDonald argue that U.S. troops “see drones as riskier and less trustworthy than manned aircraft.” In a later article, they elaborated on the details of the terms used in their survey research. They defined confidence as “the belief that unmanned aircraft can effectively complete a mission,” and trust as “the willingness to use an unmanned aircraft to complete a mission.” The crux of their argument appeared in their concluding paragraphs:
In short, [respondents] were looking for pilots with skin in the game. Without that, how could they trust the machine or the machine’s operator? … There are important, unresolved trust issues between humans and machines that make battlefield personnel wary of employing unmanned aircraft in situations in which their lives are at risk.
In other words, the claim is that troops under fire heavily view the presence of a pilot sitting inside a cockpit flying above the battlefield as an invaluable condition of establishing trust that would make ground troops willing to use a weapon system. The clear implication of their argument from the original article is that remotely-located aircrews, by definition, are structurally unable to meet this integral requirement, even when, “most [troops] knew there was a human controlling the drone, and some even knew these pilots personally.” In their second article, they back away from that angle, contemplating that some form of workaround may help build trust between crews and joint terminal attack controllers (JTACs) who call in airstrikes.
Our writing team, which includes senior MQ-1 Predator and MQ-9 Reaper pilots, including representation from the Marine Corps’ burgeoning Reaper capability and the Army’s rapidly modernizing MQ-1C Gray Eagle fleet, was unable to square their findings with our direct observations of the trust relationships they investigated. Between us, we have been involved in hundreds of JTAC-controlled engagements as well as ten thousand flight hours across eight theaters of combat. Three of us are weapons officers and four completed or are in the course of completing PhDs. We wondered why Schneider and MacDonald’s findings did not correspond to our street-level perspective of JTAC-to-aircrew trust relationships, empirical data from the U.S. combat record, or with the insights of senior military officials. We therefore feel obligated to offer analytical feedback to help improve efforts in this emerging and important area of study. We note three sources of problems that may have misled their project: lack of historical context; inaccurate conceptualization of the relationships between humans, technology, and tactics; and a series of fundamental errors in the application of specific research methods.
The Big Picture: Trust in Evolving Forms of Warfare Takes Time to Develop
Schneider and MacDonald’s assertions derive from a survey they conducted in 2014 and 2015 of JTACs and joint fires observers (JFOs). The authors stated that their findings should help shape public dialogue on autonomous weapons and human-machine teaming concepts. Jon Askonas and Colby Howard responded to the Foreign Affairs article in these pages. They questioned Schneider and MacDonald’s portrayal of JTACs, arguing that these CAS experts choose assets based on a cold calculus about capabilities, underwritten by an assessment of the crew’s proficiency, not on “warm fuzzy” feelings or the physical location of the pilot. MacDonald and Schneider’s counter included some findings from their survey instrument. Ultimately, they continued to claim that JTACs’ decisions are (at least partly) grounded in “emotional responses to machines,” affirmed their research is relevant to human-machine teaming discussions, and closed with tactical, technical, and training suggestions as “potential solutions to the trust problem.”
As with any relationship, the Predator and Reaper community had to earn the trust of their joint force partners over time. It is possible that the survey data Schneider and MacDonald collected indicate trust deficits in the past, but it would be unwise to take findings from 2014 and 2015 to inform recommendations in 2018 without appraising how much has changed over the course of three to four years. Emerging technologies hit inflection points in the pattern of their adoption: One day they’re novelties greeted with skepticism. The next day, with surprising suddenness, they become seemingly normal, everyday features of life. Measurements of attitudes in an early phase of diffusion can capture a reference point, but have difficulty forecasting future roles or utility of the technology. For example, had someone conducted a survey in 1940 about attitudes toward U.S. carrier-delivered airpower and published it in 1944, it might reveal how much views changed. But if presented as a warning that carriers were problematic, after they became widespread in their adoption, the study would seem odd and even confusing.
Similarly, one cannot offer recommendations on how to change the way Predator and Reaper aircrews do business without considering the campaign against ISIL, which began in the summer of 2014. This experience provided a confluence of tactical necessities, improved training, and refined technologies. And as far as which aircraft are preferred by people on the ground, the proof is in the pudding: As one unit commander cited in a U.S. Air Force news release stated, the endless demand for “MQ-1 and MQ-9 … close air support … as allies fought to take back [Raqqa] block by block,” when a variety of aircraft were available, indicates a preference for these systems, rather than a trust gap. Given the reputation and respect Reaper crews earned during that fight, the survey data may already have been overcome by events.
Schneider and MacDonald claimed, “operators on the ground see drones as riskier and less trustworthy than manned aircraft.” Using their definition for trust (willingness to use a weapon system), the statement conflicts with hard evidence. Publicly available Air Force data indicate JTACs have chosen to employ Predators and Reapers in combat quite often, even in the presence of other options. These choices create a problem for the researchers’ formal definition of trust — JTACs are clearly willing to use these weapon systems — but a lesser claim that JTACs prefer traditional aircraft over a Reaper is worth exploring. The on-the-ground reality is this: For all the amazing contributions that we love about what our fighter brethren provide — the high-end capabilities that guarantee air superiority, and the ability to rapidly haul loads of ordnance into the battlespace — asking them to pick off an enemy 30 meters away from friendlies in dense urban combat with civilians trapped near the fighting is often unreasonable. The smallest precision-guided munitions traditional aircraft typically carry are so large as to create a lethal blast radius upon impact that, even if centered perfectly on the enemy, includes both the target and nearby friendlies (or the enemy and the trapped civilians).Think of the precision and the relatively small warhead on the Hellfire, combined with the slow speed and long dwell of the Reaper, as the aviation equivalent of a sniper rifle.
The Reaper is relatively more capable in specific situations, traditional fighters are relatively more capable in others. Capabilities drive preferences. If you want to drop a building, trust a fighter, if you want to snipe a target in an alleyway, trust a Reaper. Professionals recommend the best capability for the desired effects, and our crews are expected to recommend fighter options when they are better choices — and as professionals, our fighter comrades returned the favor when we were the better option. The story in data looks less like a trust gap and more like military professionals matching appropriate tools to situations. In the process, they developed mutual trust through demonstrated performance over time, like any other humans in a shared enterprise.
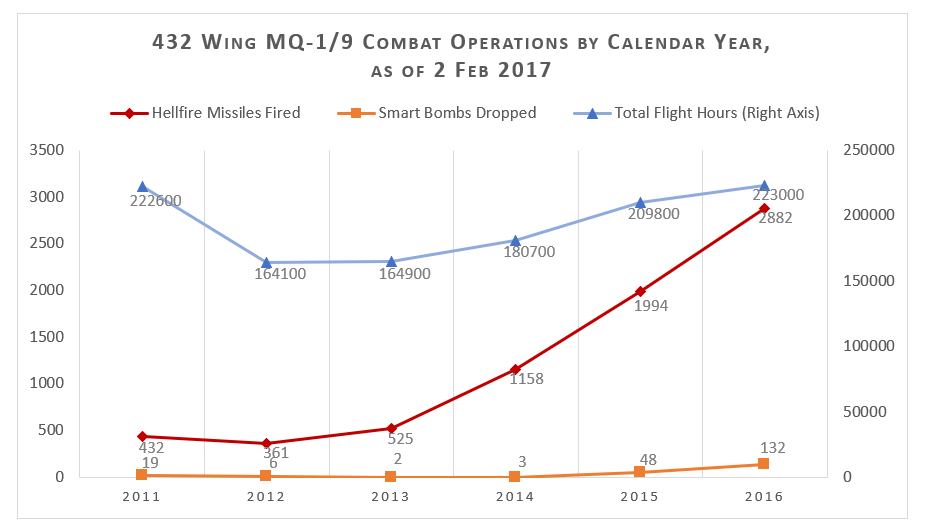
This graph depicts the number of Hellfire missile and 500-pound smart bomb attacks conducted worldwide by the 432d Wing, the Air Force’s flagship Predator and Reaper unit. From 2014 to 2015 (when Schneider and MacDonald surveyed), JTACs controlled the majority of the 1,576 annual average strikes conducted by Predators and Reapers. As the war against ISIL began in 2014, urban combat meant “airborne sniper” work was in extreme demand: These strikes grew another 74.9 percent in 2015, just as the Schneider-MacDonald survey closed. Manned airstrikes also grew exponentially during the 2015 timeframe as more fighters were deployed to the ISIL campaign.
This is what professional teamwork that surpasses membership in a specific tactical community looks like: flying a third of the Air Force’s sorties across Central Command’s area of operations, Predators and Reapers accounted for about 7 percent of strikes in 2015 and 9 percent of strikes in 2016 — but even more frequently, they found enemies and “passed the ball” to teammates. According to Col. Cluff of the 432nd Wing, Predators and Reapers were involved in “pretty much every engagement.” In the cycle from discovery to destruction, they were part of the kill-chain for 50,301 out of 61,723 strikes. In other words, just over 81 percent of the time the U.S. Air Force attacked, its enemies had been under a Reaper’s crosshairs.
Changes in the balance of which aircraft launched a weapon align with changes in the character of the fight. When the front moved quickly over open terrain, the fighters’ advantages in payload and speed often predominated. But when the fight bogged down in cities, then the Reaper’s persistence, high-resolution sensors, and hyper-precise weapon options proved more useful. Due to the increasing prevalence of urban fighting over the course of the campaign, JTACs partnered with Predator and Reaper crews so frequently that Lockheed Martin had to rapidly boost production capacity to meet Hellfire missile demand.
If troops demonstrated a strong preference against remote aircraft, or more bluntly, if Predators and Reapers were inferior options that were tolerated due to lack of other options, the percentage of Predator and Reaper strikes should have leveled or declined as the availability of manned fighters increased. But it didn’t – the number of manned fighter and Predator/Reaper strikes grew together. Moreover, Predators and Reapers “buddy lased” for fighters — guiding their weapons onto the target — more than 1,512 times. Handing off a live weapon as it’s falling toward a target is an exercise in teamwork and trust between the fighter crew, the Reaper crew, and the JTAC. Therein lies an interesting problem for the argument Schneider and MacDonald advance: JTACs had a fighter in one hand and a Reaper in the other and chose both. Schneider and MacDonald create a binary choice in their survey that does not represent the complex partnerships of the tactical world, especially as the aerial battlefield moved past the humans-versus-robots trope years ago. The pattern in data is consistent with the hypothesis that JTACs are disciplined professionals who match the right weapon and right aircraft to the right situation. It is inconsistent with the Schneider-MacDonald hypothesis.
Qualitative reports are equally incongruous with the authors’ findings. British Reapers were so successful providing close air support to marines in Afghanistan that a JTAC remarked, “the deadliest asset was the UK Reaper.” Another Marine veteran of the fierce fighting in Sangin commented, “having the Reaper on-station was the most important thing … we would not have been successful without it, hands down.” Trustworthiness was so high that Marine forces supported on the ground began advocating for organic Marine Reapers (i.e. fully integrated into tactical formations) upon their return home. Further, in response to specific urgent combat needs, marines will soon employ Reapers to “maintain the initiative and pressure the enemy to surrender, reconcile, or die.”
Schneider and McDonald claim that the “preference [against drones] was strongest in hypothetical scenarios in which the enemy was nearby and there was a high risk of friendly fire: almost 90 percent of the respondents preferred manned aircraft in such circumstances.” Yet, when battling ISIL in Sirte, Libya, over 70 percent of Reaper strikes were “danger-close” close air support missions, at times attacking within 25 meters of friendly forces. Inside “danger-close” range, friendly forces run a significant risk of injury — requiring explicit permission from the ground force commander and the highest degree of trust imaginable. The same pattern unfolded supporting JTACs in Manbij, Syria, where Predators and Reapers employed more than 300 Hellfire missiles, amounting to “approximately 40 percent of the total kinetic strikes conducted by any coalition aircraft.” In Iraq, a lone Predator stopped a massive ISIL car bomb one minute before it nearly killed 800 U.S. and Iraqi troops.
It is difficult to reconcile data suggesting a lack of trust given repeated requests for Predators and Reapers to place near-supersonic missiles at enemies within a few dozen meters of friendly positions. Particularly when Lt. Gen. Harrigian, the senior Air Force officer responsible for the aerial component of the campaign against ISIL, explained how Reapers and Predators have
been instrumental to the defeat of ISIS … importantly, the persistent reconnaissance and the ability to seamlessly transition to strike, where they’ve delivered 2900 weapons, has been a fundamental piece of the liberation and quite frankly, the success that we’ve had against ISIS.
If there were no other problems with the research, we would merely suggest that the initial article title was misleading. However, we found two other significant shortfalls: conceptual understanding of the subject matter, and execution of research methods.
Conceptual Challenges: Humans, Technology, and Tactics
Though they have yet to publish their full study, Schneider and MacDonald’s arguments thus far prompted four reasons to question their grasp of the technologies, tactics, and the roles of people involved in their research. First, they ask JTACs and JFOs about their preference to utilize “kinetic-capable (able to employ ordnance) unmanned aircraft” versus “manned aircraft.” There is, however, a thorny complication. “Kinetic-capable unmanned aircraft” sounds like a whole category or collection of things, but it really only could have referred to variations of a single design: Predator, which came in three packages — Predator A, Predator B, a.k.a. Reaper, and Predator-Sky Warrior, a.k.a. Gray Eagle. Based on one design, Schneider and MacDonald would like to make predictions about the future of a whole conceptual category (remote pilotage), for example claiming that “building better drones will not solve this problem.”
To see why that is problematic, try this thought experiment: Imagine we’re making a fruit salad for the first time and we’ve never seen fruit before. One friend brings some grapes, and then another friend brings a different kind of grapes. Other friends promised to bring oranges and apples, but they have not arrived yet. If someone asked us, “what is fruit like,” we might answer that fruit is small, green or red, and comes on a vine. Formally, this problem is called “omitted variable bias,” meaning a statistical design may be capturing something other than what its creators intended — in the case of our hypothetical, we would have no way of telling the difference between the specifics of a grape and the common characteristics of fruit. In the case of “drones,” an automated unmanned combat aerial vehicle would likely interact with a JTAC much differently than the Predator and Reaper, which use human voice communications much like traditional aircraft. It is presumptive, then, to generalize about what “better drones” might (or might not) do when we only have one very specific instance of armed “drones” to inform our current thinking.
Second, Schneider and MacDonald surveyed both JTACs and JFOs. This approach is problematic, as JFOs are not certified to employ weapons from the Reaper, Predator, or any other aircraft. JFOs can play an important role in combat by providing targeting information and an extra set of eyes to JTACs, but as the joint publication governing fire support explains, “JFOs cannot perform terminal attack control of CAS [close air support] missions, and do not replace a trained and certified JTAC.” Schneider and MacDonald claimed they surveyed “two types of military personnel” who “call in airstrikes and coordinate air support from manned and unmanned aircraft” — a factual error about basic military doctrine that results in a methodological flaw. The data presented do not measure what the authors claimed. By way of analogy, if we were surveying about motorcycle helmet use, we wouldn’t include unlicensed bicyclists and claim their answers speak to preferences of Harley owners.
Third, their proposed engineering, training, and tactical solutions to improve user trust aren’t informed by lessons learned from 15 years of combat-driven evolution. For example, they recommend using line-of-sight datalinks to increase the speed of communication between JTACs and pilots. For obvious reasons, we cannot dig too deeply into this issue in a public forum, but suffice it to say, the community actually explored the idea years ago, but found more effective and secure ways to communicate clearly in real-time with ground partners.
Similarly, the authors appear confused about the current spectrum of actual “unmanned” capabilities, wondering, “What if JTACs or JFOs were able to control unmanned platforms from the battlefield?” The ambiguity of “unmanned aircraft” makes it difficult to parse their idea. If Schneider and MacDonald have in mind small drones that provide a tactical bird’s eye view of the battlefield, JTACs and other ground troops have been controlling them from the battlefield for more than a decade. If instead they propose removing command and control of airpower from the air component and instead assigning it to the land component, then they challenge long-standing principles about the integration of air and land power, which is well outside the scope of their survey instrument, and better suited to Robert Farley’s work.
Fourth, they use an unclear conception of what constitutes “human-machine teaming” and what is just “human-human” teaming. Is it the relationship of a tank crew and their Abrams? The F-16 pilot and her aircraft? The MQ-9 crew and theirs? The JTAC and his radio or wearable computer? We acknowledge a great deal of confusion about these distinctions in both the academic literature and the public square. However, Schneider and MacDonald’s research hinges upon that distinction and therefore requires a theoretically rigorous rationale as to why JTAC-and-fighter teams are “human-human teams” but JTAC-and-Reaper teams are “human-machine teams.” In both cases, a JTAC is communicating with a human, who then uses hardware to achieve the JTAC’s desired effect. Were the JTAC giving commands to a semi-automated small UAS (such as the Wasp), that would be different, but that is more like a fighter giving commands to a missile rather than a JTAC’s conversation with a Reaper.
On that point, we recommend two authors whose work has greatly informed our own thinking on this complex topic. First, Steve Fino’s Tiger Check explores the technological and cultural changes wrought by the advent of missiles and radars in fighter aircraft. Fino holds a PhD from MIT, and is himself an F-15 pilot turned RQ-4 squadron commander; his tome should be considered required reading for any scholarly discussions of automation and aviation.
Second, MIT Professor David Mindell’s Our Robots, Ourselves provides the best scholarly treatment of human-machine interaction that we have yet encountered. Within Mindell’s model, the Reaper is just a mechanical proxy for a fellow human located somewhere else. It’s more like a telerobotic device, such as those NASA uses to support space exploration, or surgeons use to save lives far from their home hospitals: while the pilot is teaming with the remote craft, a third party doesn’t team with the proxy device, but rather with the human controlling it. Actor-network theory and socio-technical systems literature provides a wealth of insights on the complex interactions of humans and machines and how people’s interactions with one another are mediated by technology. These literatures offer a far more textured and nuanced treatment of the interplay between humans and hardware than Schneider and MacDonald’s binary distinction between “manned” fighters and “unmanned” Reapers.
Execution Challenges
Lastly, we found considerable problems in their logic of argument, sampling strategy, and statistical tests.
Social science research design must begin with a hypothesis: a falsifiable proposition that a phenomenon is at work in the world. To prove theirs, Schneider and MacDonald must show that JTACs are willing to avoid Reapers and Predators specifically because they are “unmanned.” In their second article, however, they stipulate that their “research project was not focused on establishing whether [JTACs’] perceptions were ‘correct’ or accurate representations of reality.” Their declared scope excludes causal relationships and is merely a one-time description of troops’ attitudes. Thus, the research now cannot tell anyone why troops don’t trust drones, to borrow from the title of their first article. At best, the study could only ever tell us if troops didn’t trust drones during the survey period. A claim of mistrust without explanation is unhelpful for stakeholders or policymakers: How can we reason about recommendations without understanding the nature of the problem?
Furthermore, survey validity depends upon sound sampling strategies. Beyond the erroneous inclusion of JFOs, we found three causes for concern. First, JTACs who have experience with Reapers and Predators tended to be those in special operations forces units. MacDonald and Schneider state that they included these JTACs in the study but didn’t capture special operations affiliation in the demographic data for operational security reasons. While we applaud security, that rationale is strange: The study protocol should have already protected respondent anonymity. A failure to account for this uneven concentration of experience would skew results. Second, they stated they interviewed JTACs because, “they do not carry with them the potential biases we might see from pilots of manned or unmanned aircraft, since the future of their job is not tied to investments in either.” However, in the case of marine JTACs, roughly 50 percent of their corps are actually forward air controllers (FACs), who are crews of manned aircraft. Third, interviews occurred in 2014 and 2015, but some respondents were “at the Pentagon and in think tanks,” which means that any experiences they had with Reapers and Predators took place closer to the community’s infancy.
Schneider and MacDonald’s choice of a snowball sampling strategy (having one respondent name another that you then survey, and so on in a chain reaction) amplifies this problem. It tends to concentrate samples within cliques of social networks. It’s difficult to determine whether survey answers represent the groups purportedly studied or just views from a cluster of friends, because respondents often refer researchers to associates who tend to share similar views. That’s a high-risk technique. The research MacDonald and Schneider revealed uses a difference in means test. Of the tools available to social scientists, it’s among those with the weakest protections against misleading answers when there are serious questions about inference — the underlying logic of how one factor allegedly works to cause a given outcome. It also has a clear prerequisite to use random sampling techniques, which would not be satisfied by snowball sampling. The combination of a high-risk input method and a testing procedure without robust correction capabilities makes it difficult to have confidence in the results they presented.
We look forward to seeing their full research presentation, where presumably they use some additional tools — at the very least, a logistic regression (a tool which compares the relative effect of multiple variables on a binary outcome) would account for some of these confounding variables. Without these controls, the difference-of-means test results offered in the preliminary findings mean little. Ideally, powerful tools such as structural equation models might lend credence to these findings. Panel data to control for differences in space and time would be near essential to ensuring that results were not the result of a transient tactical fad. Otherwise, we cannot generalize from the sample to the population of all JTACs.
Concluding Thoughts
The only thing that we can confidently say from the available results is that the sampled group of JTACs, based on how the survey instrument posed the question, demonstrated a preference for “manned aircraft” somewhere prior to the 2014 to 2015 survey timeframe.
A historical period where JTACs preferred not to use Reapers and Predators may have several straightforward explanations. Poor training (resulting from poor manning) might degrade combat performance. In fact, according to data in the Air Force Total Ownership Cost system, since September 2001, Air Force Predators received about 17 percent of the training time per flight hour that transport aircraft received, and less than 4 percent of what fighters received. Poor technology (such as bad radios or limited weapons loads) might sap a JTAC’s confidence in the asset. A lack of maturity in the community (endemic of any new aircraft) might result in poor tactical choices and cause breakdowns in trust. Each of these factors have been true at various times for the Predator and Reaper, as they have been for all aircraft. Today, crews are trained to much higher standards and should improve further with normalized manning levels. The successful maturation of the Predator and Reaper community over the last decade is evident in the chorus of JTACs pushing back (already published and forthcoming) against Schneider and MacDonald’s argument.
Contextual, conceptual, and statistical shortcomings seem to explain why the findings are mismatched from real-world quantitative and qualitative evidence. It would be more helpful to interrogate the causes of the alleged distrust in that population of JTACs as a social phenomenon related to the adoption of new tactical capabilities, and with a replication, to analyze why the adoption factors evidently changed. This might provide insights on how to improve the adoption of new technologies, especially with swarming on the horizon.
None of the findings support sweeping statements about human-machine teaming, the “third offset,” or how to improve close air support. Exploring differences in the human-machine teaming processes between aircrew and their aircraft might be more productive. With the advent of artificial intelligence allowing delegation of mission command to flocks of loyal wingman or skirmisher drones, these questions will become even more interesting. Secretary Mattis raised this very point: “One of the most misnamed weapons in our system is the unmanned aerial vehicle. It may not have a person in the cockpit, but there’s someone flying it … A.I. is fundamentally different.” Nick Helms, the first Predator test pilot, considered these questions in his recent article, “Trust in Autonomy.” But those answers cannot be found in the research thus far published by Schneider and MacDonald.
We conclude with a request and an invitation. First, we ask the authors for additional transparency in how they came to their conclusions about the purported absence of trust in these systems. We would like to review their survey instrument with the hundreds of JTACs and ground force commanders that have worked closely with our community. If their survey instrument is suitable, we would then replicate their design with the JTAC weapons officer and instructor corps, a population that has the twofold advantage of sampling across the entire JTAC community while representing the tactical elite of that community in their support for ground force commanders.
Second, we acknowledge numerous challenges during the rapid build-up of the Predator-Reaper community. Our observations over the past decade were of military professionals from all services working tirelessly to address problems and earn one another’s trust. Evidence abounds that the collective air-ground team succeeded. A more accurate title for Schneider and MacDonald’s findings might have been: “A Time When Some Troops Didn’t Prefer Drones.” We had the privilege of living through that transformational journey. If Schneider and MacDonald choose to explore, we believe that they too will discover a fascinating story about building trust, teamwork, technology, and tactical innovation.
Cory T. Anderson is an Unmanned Systems Technology Integration Officer in the U.S. Army Special Operations Command. He is an MQ-1C Gray Eagle Pilot who supported tours in Afghanistan and other locations. Prior to Gray Eagle, he served two tours in Iraq as an OH-58D helicopter pilot and MQ-5B Hunter sensor operator. He holds a Bachelors degree in Resource and Technology Management from Troy University and is completing his Masters of Science in Unmanned Systems at Embry Riddle Aeronautical University.
Dave Blair is an MQ-1 Predator and MQ-9 Reaper Evaluator Pilot in Air Force Special Operations Command. Prior to his time in Predators and Reapers, he served three served three tours in Iraq as an AC-130 Gunship pilot. An Air Force Academy graduate, he holds a Masters from the Harvard Kennedy School in Security Policy and a PhD from Georgetown University.
Mike Byrnes is a PhD candidate at the Fletcher School of Law and Diplomacy, Tufts University, sponsored by the Chief of Staff of the Air Force’s doctoral scholars program. Prior to his current assignment, he was an MQ-9 Reaper Evaluator Pilot in Air Combat Command. A prior-enlisted officer and Air Force Academy graduate, he holds a Masters from Carnegie Mellon University in Information Technology.
Joe Chapa is a U.S. Air Force officer and doctoral student in Philosophy at the University of Oxford. He is a senior pilot with more than 1,000 pilot and instructor pilot hours. He has published on military ethics and remotely piloted aircraft in The Journal of Military Ethics, Social Theory and Practice (forthcoming), The Journal of Character and Leadership Integration, and War on The Rocks.
Scott Cuomo is a Marine infantry officer and PhD student participating in the Commandant of the Marine Corps Strategist Program at Georgetown University. Predators and Reapers supported his marines in Iraq and Afghanistan. He has also helped design and execute multiple experiments with Reapers.
Olivia Garard is a Marine officer, aviation safety officer, and an unmanned aircraft commander. She holds an A.B. in Philosophy from Princeton University, and an M.A. in War Studies from King’s College London. Additionally, she is an Associate Editor for The Strategy Bridge and tweets @teaandtactics.
Ariel M. Schuetz is a U.S. Army officer and a student at Army Command and Staff College in the Art of War Scholars Program. She is currently writing a thesis entitled “Why the DoD is losing its asymmetric robotics advantage” and has served as the lead capability developer for Army Unmanned Aircraft Systems. Her past assignments include command of an unmanned aerial systems company in TF ODIN and multiple deployments to Operation Iraqi Freedom and Operation Enduring Freedom flying planes and helicopters. She holds a B.A. from Tulane University.
Scott “Spear” VanOort is an MQ-9 Instructor Pilot at the USAF Weapons School. He is a senior pilot with 2,000 flight hours in the MQ-1 and MQ-9 and serves as the primary editor of the MQ-9 tactics manual.
The views expressed are those of the authors and do not necessarily represent the official policy or position of the Department of Defense, the U.S. Air Force, the U.S. Marine Corps, the U.S. Army, U.S. Special Operations Command, the U.S. Air Force Weapons School, Air Force Special Operations Command, or U.S. Army Special Operations Command.
