Join War on the Rocks and gain access to content trusted by policymakers, military leaders, and strategic thinkers worldwide.


…and there he corrected many abuses and was the first to construct a wall, eighty miles in length, which was to separate the barbarians from the Romans.
— Cassius Dio, second-century Roman historian
The Wall is the Wall, it has never changed or evolved from the first day I conceived of it.
—Donald J. Trump, 45th President of the United States
Two and a half thousand years after its construction, the fortifications at Dún Aonghasa are an alien artifact — desolate rings of weather-beaten stone laid out on a windswept cliff on Ireland’s Aran Islands in the North Atlantic. But upon closer examination, Dún Aonghasa betrays sophisticated and familiar strategies of defense. These concentric walls and ditches built five centuries before the birth of Christ are flanked by a tangle of limestone stumps that serve as anti-cavalry measures called cheval de frise. It’s a location that offered a good vantage point and a safe refuge for those who held it. Dún Aonghasa presents early evidence of the same principles of redundant security measures at work in 13th century castles, 17th century star-shaped artillery fortifications, and even “defense in depth” security architecture promoted today by the National Institute of Standards and Technology, the Nuclear Regulatory Commission, and countless other security organizations world-wide.

Dún Aonghasa from the air.
Security advances throughout the centuries have been mostly technical adjustments in response to evolving weaponry. Fortification — the art and science of protecting a place by imposing a barrier between you and an enemy — is as ancient as humanity. From the standpoint of theory, however, there is very little about modern network or airport security that could not be learned from a 17th century artillery manual. That should trouble us more than it does.
Fortification depends on walls as a demarcation between attacker and defender. The very first priority action listed in the 2017 National Security Strategy states: “We will secure our borders through the construction of a border wall, the use of multilayered defenses and advanced technology, the employment of additional personnel, and other measures.” The National Security Strategy, as well as the executive order just preceding it, are just formal language to describe the recurrent and popular idea of a grand border wall as a central tool of strategic security. There’s been a lot said about the costs of the wall. But, as the American finger hovers over the Hadrian’s Wall 2.0 button, whether or not a wall will actually improve national security depends a lot on how walls work, but moreso, how they fail.
The Wall
Walls are binary. They protect us from them (or them from us). But by setting up a barrier, a wall instigates a contest between attacker and defender — for a thief, a locked door is just a design challenge. This means that advances in walls bring with them corollary advances in weapons. At the root of fortification is the idea that you can out-calculate an opponent. Fortification supposes that through preparation, diligence, and ingenuity, a place can be made strong enough that it would cost an enemy too much to take it. It’s such a ubiquitous approach to security that some historians have claimed it as an essential principle of nature. If Trump’s wall is so much Ozymandian fantasy, it’s at least an ancient fantasy. The 8th century earthworks of Clawdd Offa still demarcate the boundary between Wales from England. Over millennia, a cycle of fortification, siege, collapse, and innovation has developed. Ancient motte (hill) and bailey (wall) castles foreshadowed siege engines, and the most imposing castle walls prophesied the advent of artillery. Quantum computing is distant thunder to data encryption.

Restormel Castle, a 12th-century shell keep built over an old wooden motte and bailey castle. (Darren Shilson/Flickr)
In the 19th century, architect and engineer Violet le Duc saw this as a Darwinian struggle, propelling the fittest nations forward. He put it starkly:
War is struggle, and we find struggle everywhere in nature; it secures greatness and duration to the best educated, the most capable, the noblest, the most worthy to survive. And in the present day more than ever, success in war is the result of intelligence and of that which develops intelligence—Work.
Here conflict is anabolic. In this view the evolution of simple to complicated fortification is a symptom of greater societal advance. The earliest and simplest remnants of fortifications changed in the 1200s when evolutions in weaponry drove continued innovation and complications in medieval castles. In 1494, during the First Italian War, the introduction of mobile field artillery allowed Charles VIII of France to overthrow in just weeks castles that might have held out for years only a century before.
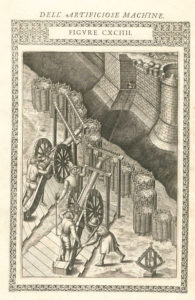
Late 16th-century plate: depicting artillery against an older castle design.
The innovations in artillery technology prompted immediate and drastic changes in how walls were built. Ingenuity applied to defense quickly countered the momentary primacy of attack. By 1528, Michelangelo Buonarroti and Leonardo Da Vinci had both created dramatically new fortress designs. They dropped the high, brittle castle walls in favor of lower, sloping walls designed to deflect and absorb cannon shot. Their perimeters show angled bastions instead of the geometric quatrefoil towers of the medieval era. This eliminated blind spots and improved a fortress’s ability to attack back, permitting each angled bastion to defend the other. Innovation in response to threat ushered in a new era of scientific warfare, as 16th and 17th century fortress design and siegecraft became increasingly engineered and calculated efforts.

Sketch of fortifications of Porta del Prato in Florence (ground floor plan), Michelangelo, c. 1525.
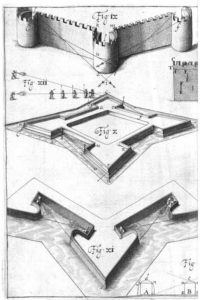
Elimination of quatrefoil dead space illustrated by Matthias Dogen, 1647.
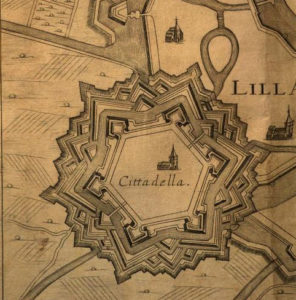
The citadel at Lille, 1673.
There is an eternal arms race between attack and defense. Better walls demand better weapons demand better walls — ad infinitum. This evolutionary courtship of the siege and the fortress is one of apparently limitless pursuit. From the present vantage point, it’s worth noting what has changed, and what hasn’t. Learning to read a fortress, you can see evidence of a strategist engaged with a problem. Each feature of the fortress is at once an expression of desire to protect something and a counter to the possibility of some threat. One of the 2017 contractor design prototypes submitted for the U.S. border wall draws explicitly, if crudely, from the fortifications of medieval castles, including a “talus” or angled portion at the base of the wall. The talus was designed to keep siege towers at a distance from the walls, making it easier to defend, and harder to extend ladders or walkways. The principle for the prototype is the same.
Fortresses are a kind of marker that indicates the state of struggle. So why does a bronze-age stockade so closely resemble network security architectures and facility perimeters in place two millennia later? The linear advancement of fortresses hasn’t dodged the basic rules of the game: attacker, defender, and innovation on each side.
The Perimeter Paradox
Walls don’t fail gracefully. But there is a bewitching tendency to trust them more than we should, and this leads to dangerous liabilities. Extreme risk prognosticator Pasquale Curillo calls this tendency to depend too much on controls we’ve put in place the “fence paradox.” By protecting things — which they must — organizations can encourage situations where they stand to lose a lot if their wall is breached. When that fortification fails (and eventually, every fortress fails) it fails catastrophically. The scale of the Equifax hack in 2017 and the Brussels bombings in 2016 both illustrate the way that organizations and systems organize risk, tending to put together massive targets for potential threats. Walls actually encourage this kind of thinking. If you build walls to protect something, it makes sense to expect them to work. But network architects and airport security designers both need to listen to de Montluc, the 16th century French military mastermind: “Nothing is impregnable.”
We need a new awareness of what walls do. It’s tempting to think of them as blocking threats, but they don’t. They behave more like filters — winnowing out only those threats not serious enough to circumvent them. And this implies a secondary problem apart from the fence paradox. A wall that prevents large-scale foot traffic across unsecured locations in the U.S border means that only determined, capable adversaries will be able to cross the wall. The people who are the least threatening are the only ones who are easily deflected. It may prevent smaller scale losses, but it actually encourages your biggest threat to innovate, leaving room for catastrophe. Bag checks and barricades moved a perimeter outward at the Mandalay Bay Casino last October, but Stephen Paddock circumvented this by moving his position upward. As Washington considers the marginal benefits of a massive border wall, it needs to think equally of this revenge effect.
This weakness is where the idea of “defense in depth” (layered security) comes from. A good summary of the reasons for defense in depth comes from a 1921 Infantry Journal, published by the U.S. Infantry Association: “All essential elements of the defense should be organized in depth. If the forward defensive areas are captured, resistance is continued by those in the rear.” Rather than relying on a single perimeter, the bronze-age security strategists at Dún Aonghasa recognized the need for multiple layers. It’s a form of spatial risk management, applying progressively robust layers to security architecture. This concept, however, only forces the adversary’s focus. Persistent enemies find ways to the center, from which they can do immense damage because defense in depth tends to concentrate risk at the center.
Risk created by centralization was behind the Germanwings 9525 crash in 2015. Because of security measures put in place to protect against breaches of the cockpit, the pilot was able to lock himself in the cabin and intentionally crash a plane, killing 144 passengers and 6 crew members. Perimeter security measures and the necessity to trust the pilot illustrate more broadly the problem with fortifications: Protective measures create massive centralized risk.
Building a border wall may seem simplistic, or a failure to address the real adversary, but the concept of a grand defensive wall isn’t just ancient, it’s still central to the way we do all kinds security. The problem may be less with the wall itself, for what it is, and more with the fact that we keep depending too much on fortification and, by doing so, centralizing risks.
Un-Fortress Federalism
The tangled distribution of efficient power in American government makes grand national security initiatives tough to implement. It’s a fortress-resistant arrangement. James Madison explained the limits of federal powers this way in Federalist 39:
…local or municipal authorities form distinct and independent portions of the supremacy, no more subject, within their respective spheres, to the general authority, than the general authority is subject to them, within its own sphere.
As much as this frustrates attempts at unilateral national security solutions, it also serves as the basis of a certain kind of protection. American government is structurally, and by design, prevented from building monolithic fortresses. The idea behind compartmentalization (limited access) and limited privileges in information security operates on a similar principle. If one wall is breached the amount of damage is limited. Rather than conceiving of security in layers, the constraints of federalism impose a network that is inefficient but less prone to catastrophe. This limits the size of any one fortress. It also limits the degree to which you establish vulnerabilities that depend on these fortifications. In December 2015, it took well-resourced hackers — precisely the ones to worry about — using stolen credentials to gain access to and shut down portions of the Ukrainian electric grid. The Ukraine cyber-attack — while highlighting urgent cybersecurity challenges — occurred on an electric grid with a comparatively uniform makeup, compared to what would be found in the United States. It would be difficult to replicate the attack in the United States, given the private, public, and regulated entities in the United States that make the target that much more complex.
To Build or Not
If a massive border wall seems like a bad idea and waste of money, there’s a more disturbing fact beneath it: Almost every current approach to security — from bag checks to passwords — already depends too much on walls. Border wall skeptics owe the same coldly rational criticisms to other, less politically charged walls. Over-reliance on walls has been a persistent security tendency throughout human history, and yet, their strategic effectiveness is checkered. The Maginot line is often remembered as a failure — a massive national investment in border security that the invading German army simply drove around. Hadrian’s wall was repeatedly breached and abandoned, arguably not worth its cost. Walls as tools of national security policy are largely a history of failed states.
Security cannot depend on the hope that a fortification will not fail. Eventually, and always, walls fail us. This ought to make us humble about our fortification aspirations and reduce our expectations for them. Plato reckoned that walls encourage “a soft habit of soul in the inhabitants, by inviting them to seek refuge within it instead of repelling the enemy.” Aristotle retorted, that not building walls was “like desiring the country to be easy to invade.” It’s still an open argument.
Jack Anderson has over a decade of experience in a broad range of security and disaster response roles spanning private industry and public service, including infrastructure protection, insurance investigation, counterterrorism, catastrophe and crisis response, post-disaster forensics, and risk management. He holds an M.A. in Security studies from the Naval Postgraduate School and currently serves as a senior analyst at the U.S. Department of Homeland Security. His writing has appeared in The Wall Street Journal, Homeland Security Affairs, and a few other places.
The views expressed here are solely the author’s and are not endorsed by the U.S. Government. This article was submitted and approved through his agency’s pre-publication process.
Image: Wikimedia Commons
