Join War on the Rocks and gain access to content trusted by policymakers, military leaders, and strategic thinkers worldwide.


In March 2016, seven Iranians affiliated with the Islamic Revolutionary Guards Corps (IRGC) were indicted for a coordinated cyber campaign against the U.S. financial sector. The campaign is described as a direct assault on 46 of the country’s largest financial institutions. Imagine if instead of waiting for a government response and correct attribution, all 46 banks decided to take matters into their own hands. What if each bank independently attempted to digitally counterstrike, but did not know whom they were fighting back against? In this case, they would be attacking the IRGC, and could unwittingly escalate already high tensions. A bill introduced this year, and updated in October, would enable exactly this kind of scenario where corporations would be allowed to “hack back” following a cyber attack.
The “hacking back” debate in cybersecurity has resurfaced several times this year in the form of the Active Cyber Defense Certainty Act (ACDC). Now a bipartisan proposal by Reps. Tom Graves (R.-Ga.) and Kyrsten Sinema (D.-Ariz.), the latest version of the bill aims to give corporations improved self-defense capabilities in the cyber domain by allowing them to enter an external network without authorization. The bill represents a response to the ongoing wave of cyber attacks against U.S. corporations. Ransomware brought in over a billion dollars in 2016, and reputational damage from data dumps has hit corporate profits and led executives to step down. Most recently, the discovery of North Korean hackers, Iranian-linked APT 33, and Russian-linked Dragonfly within various energy companies is a reminder of the constant threat to critical infrastructure. While this is clearly not a sustainable path, the ACDC is not the solution to these growing cyber threats. The bill risks greater escalation and opens the door to a range of unintended consequences that could make cyberspace more dangerous.
Background
The thirty-year-old Computer Fraud and Abuse Act (CFAA) prohibits anyone from accessing a network without authorization. The technological and geopolitical landscape look remarkably different today than they did in 1986, but policy and law have been slow to catch up to these changing realities. In fact, there are numerous anecdotes of “cyber vigilantism,” where corporations are already taking steps to find and delete the stolen data, such as potential retaliatory hacking by banks. With this rise of concerns over vigilantism, it is not surprising that the ACDC was proposed earlier this year to allow the private sector to enter attacker networks unauthorized, which is often referred to as hacking back. An updated version of the act was released following the WannaCry ransomware attack in May, which impacted hundreds of thousands of machines in over 150 countries.
The notion of hacking back has slowly been gaining traction within the private sector as the pace and scale of attacks continue to rise, coupled with perceptions that the government is not doing enough to protect them. Consider how many times the government has publicly attributed and responded to an attack in the last few years. It has only been a handful of times. Major breaches, including those against Target and Equifax, have not been publicly attributed and for those that have, such as Yahoo, the indictments are viewed as more symbolic than consequential. Similarly, some may believe hacking back could provide a deterrent against future attacks, although it is questionable how much this would impact ideological, profit-seeking, or generally malicious activity. Given the feeling of helplessness, coupled with the desire for retribution or simply to retrieve stolen data, many in the private sector continue to seek additional ways to respond to cyber attacks.
Key Concerns
Technical analyses and expert discussions have debated the merits of hacking back, with many in the cybersecurity community expressing concerns that this bill would do more harm than good. In fact, in a recent poll, over 80% of cybersecurity experts advise against the practice. The concerns fall largely into two categories: questionable efficacy and the risk of escalation. First, it is unlikely that hacking back would prevent a company’s data from being disseminated or manipulated. The average time between when a compromise occurs and when a corporation discovers it is roughly 100 days. In addition, under the ACDC, victims must notify the FBI before using offensive cyber measures, which are then placed in a queue for bureau review. Greater collaboration between corporations and the government is essential for cyber defense, but under the ACDC framework, the hack back could require an additional lag in response. Therefore, even in the best cases of early detection, the attacker still has plenty of time to copy the stolen data. If an organization were to hack back, it is highly unlikely it would recover the only copy of its data.
In addition, attribution is extremely difficult, especially for most private-sector entities, which generally lack the necessary technical resources and knowledge of the adversary. Therefore, there is no guarantee against a defender hacking back at the wrong machine. False positives, framing and deception within code, such as the planting of a foreign language, and various technical challenges make it very difficult to know who really committed an attack. In cases of self-propagating worms such as WannaCry, there may not be command and control or exfiltration servers, which leaves a lot of ambiguity regarding who or what to hack back. When the ACDC’s second version was introduced in May, Graves noted that his bill may have prevented the WannaCry attack. In fact, though, because there was no “human in the loop” controlling the worm as it spread, hacking back against WannaCry could have led to attacking innocent victims. Attackers also often include additional nodes and third-party access to hinder attribution, causing defenders to enter a series of innocent networks that were unknowingly part of the attack. Even if the attacker is identified with a degree of certainty, it still requires a great deal of resources to conduct an offensive campaign. Nation-states spend years on these kinds of campaigns, with resources that most corporations lack.
Perhaps the more important cause for concern is the potential for escalation of conflict. The ACDC focuses on criminal activity, and wrongly assumes that the attackers are always criminal groups. Graves notes, “The certainty the bill provides will empower individuals and companies to use new defenses against cybercriminals.” This ignores the persistent onslaught of attacks against corporations by nation-states and nation-state affiliated groups. The ACDC does prohibit corporate attacks against government computers, but it is not clear whether the prohibition refers to U.S. or foreign governments. Regardless, given the challenges of attribution, a company could inadvertently attack a network belonging to a foreign government (remember the IRGC example). Even the most well-resourced corporations are unlikely to fare well against China’s PLA Unit 61398, Russia’s APT 28, Iran’s APT 33, or North Korea’s Unit 180.
There also are instances of government-linked hackers who may attack in their spare time, or are loosely affiliated with governments, but are not acting as agents of the government. The revised ACDC does not legalize hacking back against government computers, but in many instances, it may be hard to tell what a “government” computer is. Ambiguous affiliations could result in escalating tensions if organizations attack what they believe to be lone wolves, when in fact they are government-affiliated.
Whether the attacker is a criminal group or nation-state, or even a lone wolf, the risk of tit-for-tat escalation is high. When the Atlantic Council think tank simulated a geopolitical event that included hacking back, it found that the practice quickly escalated existing geopolitical tensions.
The ACDC attempts to offset the potential for escalation by prohibiting the violation of laws in other countries. Assuming corporations have scholars with expertise on the legal cyber frameworks across a multitude of countries, they also have to know the exact location of the attacker, which, as noted earlier, can be extremely difficult.
Finally, cyber attacks are just one form of digital response that these groups could use in response to a hack back. These attacks are often part of a coordinated campaign coupled with bots and disinformation. When a company hacks back, even if it has accurately attributed the source of the attack, it risks triggering retaliation not just from cyber warriors but also trolls, which can inflict large-scale brand, reputational, financial, and even physical damage. And that doesn’t even touch upon potential responses outside of the cyber domain, such as targeted economic punishment or even military conflict. The potential for collateral damage is exceedingly high.
The authors of the latest version of the bill attempted to address concerns from the cybersecurity community, especially regarding the unintended consequences if things go awry or a counterstrike misfires. In dictating what defensive measures corporations are allowed to engage in, this version of ACDC includes intent, which was largely absent in previous versions. That is, the act prohibits intentionally destroying information or rendering it inoperable; intentionally exceeding activity beyond reconnaissance; intentionally accessing an intermediary’s computer; and intentionally disrupting internet connectivity resulting in damages. Unfortunately, the inclusion of intent does not prevent unintended escalation from happening. In fact, it actually expands the range of activities corporations could undertake because they can always claim their retaliation was unintentional, and proving intentionality would be extremely difficult. Moreover, despite the best of intentions, things can go wrong — data and machines can be inadvertently damaged.
If Not ACDC, Then What?
The latest version of the ACDC, introduced on Friday, Oct. 13, coinciding with cybersecurity awareness month, rightly notes the limited efficacy of current laws against cyber crime, and the need to modernize the CFAA to address the prevalence of cyber-enabled crime. But while the CFAA and cyber policy in general desperately need to be modernized to better equip defenders, the ACDC is not the answer.
The ACDC act reflects the reality that corporations that are attacked have little recourse. Although the bill has yet to be debated on the floor, its persistence this year is cause for alarm. One reason for its staying power is the policy vacuum in cyber strategy and leadership. Because the CFAA is thirty years old and ill-equipped to address modern threats, combined with the dearth of guidance for handling these attacks, the ACDC act has emerged to address these shortcomings. As Sen. Angus King (I-Me.) has often noted, “The country has no strategy or doctrine around cyber attacks.”
Instead of legalizing hacking back, the government should focus on filling this policy vacuum by formulating a comprehensive cyber strategy or doctrine. This should include a coherent declaratory policy, specifying which responses are available for which types of attacks. Or, as King simplified in a recent Senate Armed Services Committee hearing, the United States needs to determine “if x, then y.” Too often, policymakers take the myopic view that a cyber attack requires a cyber response, but that is simply not true. Instead, a declaratory policy based on the effects of the cyber attack can provide the U.S. government with a range of responses across the diplomatic, information, military, and economic domains.
In addition, the declaratory policy should inform deterrence frameworks, shaping U.S. strategies and defenses to deter adversaries from achieving particular effects (e.g., destruction of critical infrastructure) via digital attacks. Deterrence frameworks require a credible commitment to respond if those attacks and effects occur. This must not only occur at the national level, but at the international level as well. These frameworks should also rely on more resilient defenses, including innovative means to quickly support the private sector when an attack occurs. Estonia’s national guard is a good example of public-private sector coordination to strengthen cyber defenses, and the model has been mirrored in some states, such as Maryland.
Simultaneously, U.S. leadership is necessary to shape global rules of the road, or norms. Norm creation has been underway for years, but has recently stalled. Strong U.S. leadership will be needed to push forth norms for a free and secure internet, otherwise other actors will fill the leadership vacuum. Clearly, norms will do little to stop information operations, such as those by Russian trolls, or to deter countries leveraging the asymmetric advantages of cyber attacks, such as North Korea. Nevertheless, they are essential to prompt initial steps toward consensus on what is and is not appropriate activity in cyberspace. Importantly, this should include reinforcing the notion of the state’s monopoly on the use of force, and limiting other countries from similarly pursuing private-sector hack-back capabilities.
When crafting these frameworks and policies, a consensus must be reached on the key terminology. The ACDC rationalizes hacking back as a form of “active defense,” which is problematic. As a recent George Washington University report concluded, the two should not be used interchangeably. The thorough study recommends the taxonomy below, which could be a useful starting point for shaping policy responses and guidelines. To simplify this spectrum of activity: Passive defense refers to traditional defenses that defenders can install in their own networks, such as anti-virus software designed to detect and prevent malicious software. This is essential, but no longer enough to stop the range of attacker tactics, techniques, and procedures. As a result, a gray zone of active defense has emerged in which defenders take proactive measures inside their networks. This includes hunting within networks to actively catch intruders. Honeypots, or traps used to lure in attackers, are another way to more proactively catch attackers while remaining within your network.
Importantly, hacking back does not fall within either of these categories. Instead, it pertains to “offensive cyber,” or activities external to an authorized network. This is not merely a wonky debate, but has enormous implications when differentiating between behavior within an authorized network and activities external to it. As discussed, entering an unauthorized network — hacking back — entails significantly different consequences and risks.
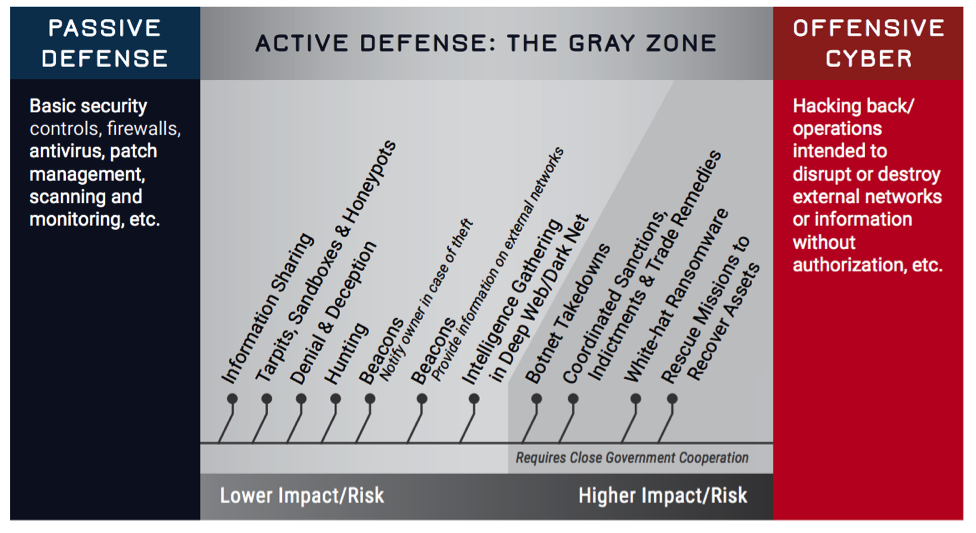
Image source: Into the Gray Zone: The Private Sector and Active Defense Against Cyber Threats
As Admiral Mike Rogers expressed to the House Armed Services Committee, hacking back simply puts “more gunfighters out on the street in the Wild West.” Clearly, the CFAA needs modernization to reflect modern technological realities, but legalizing hacking back is not the answer. Taking the steps toward a coherent, declaratory cyber strategy and norm formulation is much more challenging than simply permitting companies to retaliate, but it is necessary for both national and economic security. Absent such a framework, the cyber domain will remain plagued by attackers acting with impunity, the private sector will remain easy targets in the asymmetric power balance, and the potential for collateral damage will only grow.
Andrea Little Limbago is the Chief Social Scientist at Endgame, where she researches the intersections across geopolitics, cybersecurity, and data science, and directs the company’s technical content. She has previously worked in academia and at the Department of Defense. Andrea earned a PhD in Political Science from the University of Colorado at Boulder, where she taught international relations and foreign policy courses.
Image: FBI
