Join War on the Rocks and gain access to content trusted by policymakers, military leaders, and strategic thinkers worldwide.


Security industry promoters and a zealous yet ill-discerning press corps make it easy to believe that state-sponsored cyber-attacks have reached epidemic levels. The convenience of the term “attack” and its impression on the psyche belie a subtly fundamental question: What is a “cyber-attack,” anyway?
When I tell people that I lead FireEye iSIGHT’s “Attack Team,” I am sometimes met with stares of disbelief. But I quickly confess I do not lead cyber-attacks at all. I study them, think about them, and write about them.
To my team and me, an attack is not an intrusion. It’s not a compromised machine. It’s not stolen intellectual property, embarrassing leaks, or credit card numbers. To us, an attack is delivering the blow. It’s an effort to destroy, degrade or deny access to a computer system or to manipulate the physical, real-world processes – like electricity transmission or distribution – that computers control.
Intrusion or exploitation of a computer system often precede an attack, but serve a different objective – to gather information. To illustrate: Intruding into networks to steal blueprints of a nuclear weapons facility is exploitation. Delivering a worm that manipulates the nuclear enrichment process at that facility is an attack because its objective is to degrade or destroy.
The Scorecard
Relying on this definition and open-source reporting, our team identified 17 occasions on which state-nexus perpetrators attacked organizations in other countries. Four countries conducted the attacks, and seven have been attacked. We use the term “state-nexus” to imply consistency with the interests and capabilities we expect of the perpetrator country, without confirming that military or intelligence services conducted or ordered the attacks.
It is also important to note that this selection of attack events excludes certain destructive activities. First, while the capability to destroy data is a common characteristic of remote access trojans and similar intrusion tools, it is not uncommon for adversaries to wipe computers or information to inhibit investigation of their activities. We make a distinction between this type of clean-up and “wiper” attacks, in which destruction of data is a core intent. Second, electromagnetic attacks, such as jamming radios, are not included in our definition even though these may fall under the broad concept of cyber-attacks. Finally, we are highly confident that the publicly noted events we identified through open-source data are only a small portion of total state-nexus attacks that have occurred.
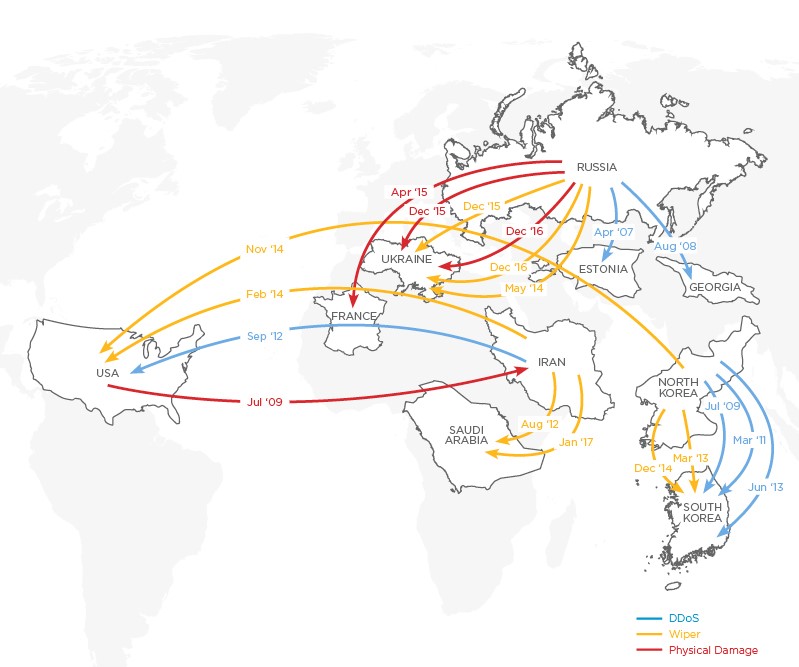
Figure 1: Cyber-attack perpetrators and victims (Source: FireEye)
Longitudinal analysis of the attacks originating from the four primary actors (the United States, Russia, Iran, and North Korea) shows significant differences in capability, but suggests a common evolutionary path.
U.S.-nexus actors have visibly participated in just one attack: the Stuxnet incident around July 2009. In a pre-emptive cyber strike, Stuxnet disrupted uranium enrichment centrifuges allegedly used in Iran’s military nuclear program, carefully avoiding impact on civilians or private systems. Stuxnet occurred nearly six years before any other state-nexus group achieved physical consequence via a cyber-attack, underscoring U.S. leadership in the cyber domain.
Russia-nexus actors have participated in six attacks, one against Estonia, one against Georgia, one against France, and three against Ukraine. Retrospectively, the relatively unsophisticated distributed denial of service (DDoS) attacks on Georgia in 2008 and Estonia in 2007 presaged the development of more formalized state-nexus cyber-attack capabilities, aiming for both disruptive and psychological impacts. These events coincided with Russian state objectives, but ostensibly relied on Russian nationalists acting without official state sponsorship.
In May 2014, Russia-nexus actors debuted cyber-attacks to destroy Ukrainian election results, which we can now recognize as an indication of Russia’s application of computer-based attacks to impact foreign elections.
Three of the six Russia-nexus attacks resulted in physical effects. In April 2015, an attack destroyed media broadcast equipment belonging to France’s TV5Monde. While the motive remains obscure, it may have simply been a test of capability. In December 2015, an attack against several regional electricity distribution firms knocked out power to at least 225,000 customers in Ukraine. In December 2016, an attack against a Ukrainian transmission firm took out power to a section of Kiev. This appeared to be part of a larger campaign that also disrupted financial transactions and rail shipments.
Iran-nexus actors have participated in four attacks – two each against Saudi Arabia and the United States. In our view, Iran has yet to intentionally cause direct physical impact via a cyber-attack, A round of wiper attacks that we call “Shamoon Returned” near the end of 2016 and the beginning of 2017 destroyed data at various organizations within Saudi Arabia. The first round of Shamoon attacks, in August 2012, wiped the data from 30,000 computers at petroleum giant Saudi Aramco and affected neighboring Qatar’s Rasgas. In September 2012 Iran-nexus perpetrators attacked a U.S.-based hospitality firm as presumable retribution for bellicose comments made by a pro-Israeli businessman. Additionally, the country was allegedly behind large-scale DDoS attacks against U.S. financial institutions the same month.
North Korea-nexus actors have participated in six attacks, making them the most prolific in terms of pure numbers. However, two-thirds of these were DDoS, and the other pair involved wiper malware. Five of the attacks impacted South Korea, and one affected a high-profile entertainment company in the United States as retribution for a film unfavorable to their supreme leader. Like Iran, North Korea-nexus attacks have yet to verifiably cause physical damage.
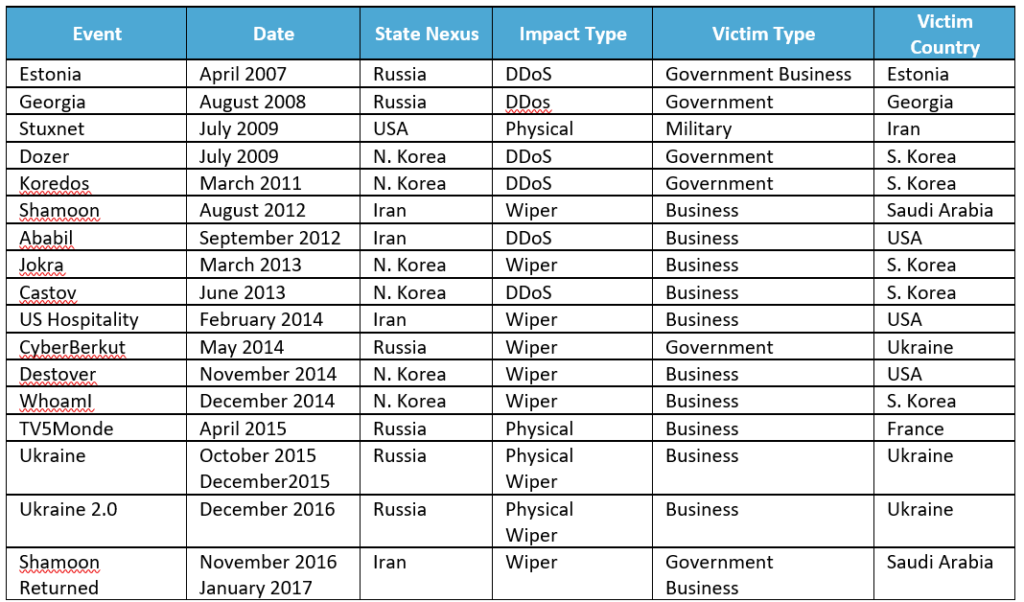
Table 1: Publicly noted attack events (Source: FireEye)
Despite the small sample, when examined over time, we note that attacks are becoming increasingly visible and virulent. With the exception of the 2009 Stuxnet attack, the chart below exhibits a trend line towards more severe effects—indicating that nation-states are increasing their cyber-attack capabilities. Only Russia-nexus actors have visibly attacked various economic sectors of a target nation at the same time, in the case of Ukraine in 2016.
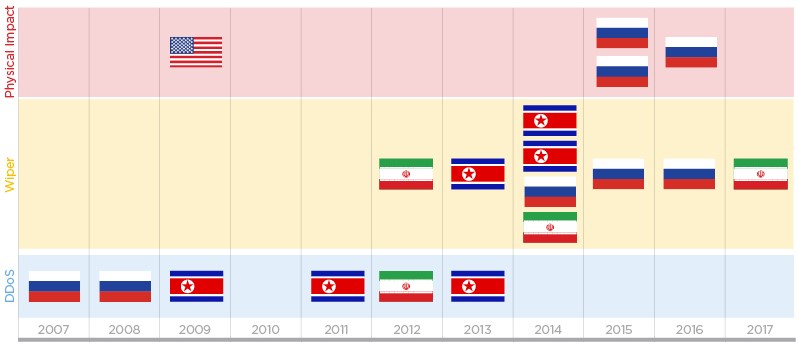
Figure 2: Timeline of attack events by capability demonstrated, with flags representing perpetrator countries (Source: FireEye)
Who Scores Next?
Reasoning from the data and incidents analyzed, we believe state-sponsored attacks will most frequently occur against businesses in locations of recognized geopolitical conflict. All of the events – except TV5Monde – occurred in areas of pre-existing geopolitical conflict (e.g., between North Korea and South Korea, between Russia and Ukraine, and between Iran and Saudi Arabia), and 12 of the 17 attacks struck business—rather than only government or military—targets.
We anticipate that victim nation-states will feel compelled to acquire capabilities to respond in kind, eventually increasing the number of states engaging in cyber-attack operations. History shows that states frequently adopt new armaments after observing that they are useful to others. We suggest that nation-states already engaging in cyber espionage will find it simple to adjust their tools to conduct attacks with destruction as their primary motive. The know-how to acquire attack capability is freely obtainable in open sources, though its formalization requires effort.
Based on this analysis, our team suggests that states acquiring cyber-attack capabilities will follow the same historical trajectory of maturity outlined above: moving from DDoS to data destruction, and then to physical effect. This pattern is consistent with increasing investment and operational scale.
As policymakers and risk executives prepare their governments and organizations against cyber threats, a clear conceptual definition of “attack” enables them to discern the important from the mundane. Familiarity with the circumstances in which nation-states have publicly exhibited their cyber-attack capabilities empowers leaders to more accurately assess when their organizations face heightened risk.
In a world where imposing physical consequences via computer attack is no longer just a theoretical capability, the ability to quickly identify a breach, reasonably attribute the intrusion to a specific actor, and immediately invoke carefully conceived incident containment and response plans is sound defensive play.
Sean McBride’s Attack Synthesis Team at FireEye iSIGHT Intelligence fuses in-the-field collections with geo-political context and technological expertise to provide timely and dependable finished intelligence.
